1# Perfetto security model 2 3*** note 4**This doc is WIP**, stay tuned. 5<!-- TODO(primiano): expand security model doc. --> 6*** 7 8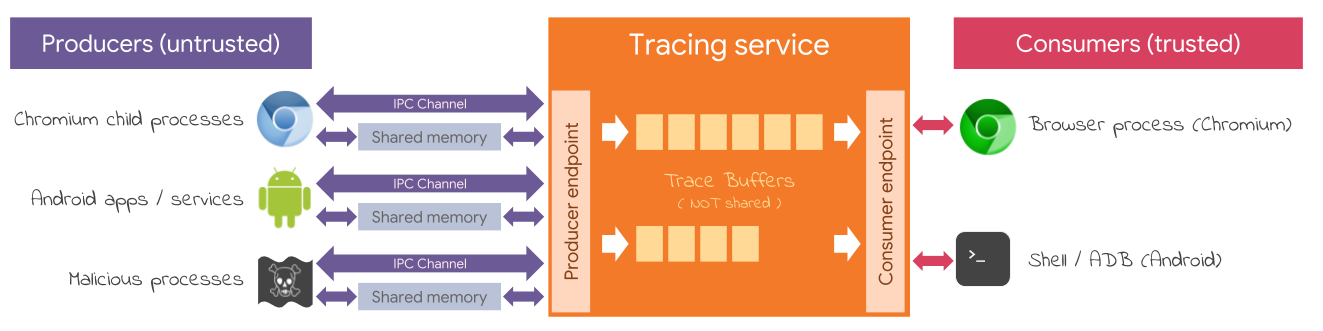 9 10**TL;DR** 11The tracing service has two endpoints (in Chromium: Mojo services, on Android: 12UNIX sockets): one for producer(s) and one for consumer(s). 13The former is typically public, the latter is restricted only to trusted 14consumers. 15 16**Producers** 17Producers are never trusted. We assume they will try their best to DoS / crash / 18exploit the tracing service. We do so at the 19[core/service_impl.cc](/src/tracing/core/service_impl.cc) so that the the same 20level of security and testing is applied regardless of the embedder and the IPC 21transport. 22 23**Tracing service** 24- The tracing service has to validate all inputs. 25- In the worst case a bug in the tracing service allowing remote code execution, 26 the tracing service should have no meaningful capabilities to exploit. 27- The tracing service, by design, has a limited syscall surface to simplify 28 its sandboxing: 29 - It doesn't open or create files (% tmpfs). 30 - It writes only onto file descriptors passed over the IPC channel. 31 - It doesn't open or create sockets (on Android the IPC sockets are passed by 32 init, see [perfetto.rc](/perfetto.rc)) 33 - On Android it runs as nobody:nobody and is allowed to do very little 34 see [traced.te](https://android.googlesource.com/platform/system/sepolicy/+/master/private/traced.te). 35 - In Chromium it should run as a utility process. 36 - TODO: we could use BPF syscall sandboxing both in Chromium and Android. 37 [Proof of concept](https://android-review.googlesource.com/c/platform/external/perfetto/+/576563) 38 39**Consumers** 40Consumers are always trusted. They still shouldn't be able to crash or exploit 41the service. They can easily DoS it though, but that is WAI. 42 - In Chromium the trust path is established through service manifest. 43 - In Android the trust path is established locking down the consumer socket 44 to shell through SELinux. 45 46**Shared memory isolation** 47Memory is shared only point-to-point between each producer and the tracing 48service. We should never ever share memory across producers (in order to not 49leak trace data belonging to different producers) nor between producers and 50consumers (that would open a hard to audit path between 51untrusted-and-unprivileged and trusted-and-more-privileged entities). 52 53**Attestation of trace contents** 54The tracing service guarantees that the `TracePacket` fields defined also in 55[trusted_packet.proto](/protos/perfetto/trace/trusted_packet.proto) cannot be 56spoofed by the Producer(s). Packets that try to define those fields are rejected 57(modulo the clock snapshots). 58See [PacketStreamValidator](/src/tracing/core/packet_stream_validator.cc) and 59[its unit test](/src/tracing/core/packet_stream_validator_unittest.cc) for more 60details. 61At the moment nothing prevents that a producer writes `TracePacket(s)` that do 62not belong to its data sources. Realistically the service will never prevent 63that because doing so would imply that the service knows about all the possible 64types of packets, which doesn't scale. 65However, the service appends the POSIX uid of the producer to each `TracePacket` 66to perform offline attestation of the contents of the trace. 67 68Internal docs 69------------- 70* [Android security review doc](http://go/perfetto-asec) 71* [Chromium security review doc](http://go/perfetto-csec) 72